
Exciting new series on “Voice, Body and Movement for Lawyers – How to connect with the jury and find Justice Through Dramatic Technique!”
Click here to find out more
Public and private entities are presented with, and urged to implement, new technologies on a regular basis. At the same time, officers or employees may use new technologies such as ephemeral messaging apps that are part of existing IT systems and become “shadow IT.”
This session will examine possible use cases for new technologies, how these might be evaluated, the pros and cons of adopting new technologies. The session will also suggest a checklist to use when looking at new technologies.
Philip A. Greenberg, Esq., who has been a litigator in the State and Federal Courts for 52 years, ha...
State attorneys general continue to play a central and increasingly aggressive role in consumer prot...
This program focuses on asylum claims based on sexual orientation, addressing the unique clinical, c...
This course analyzes federal contractor cyber security obligations under the Federal Acquisition Reg...
My contract was terminated and the contracting officer did not pay my invoices – what can I do...
This interactive course is designed to equip legal professionals with the knowledge, tools, and stra...

Trademark doctrine was built for a marketplace that no longer exists, leaving practitioners to litig...
Over the past year, the Patent Trial and Appeal Board (PTAB) has undergone a dramatic policy shift r...
Contracting with the Federal Government is not like a business deal between two companies or a contr...
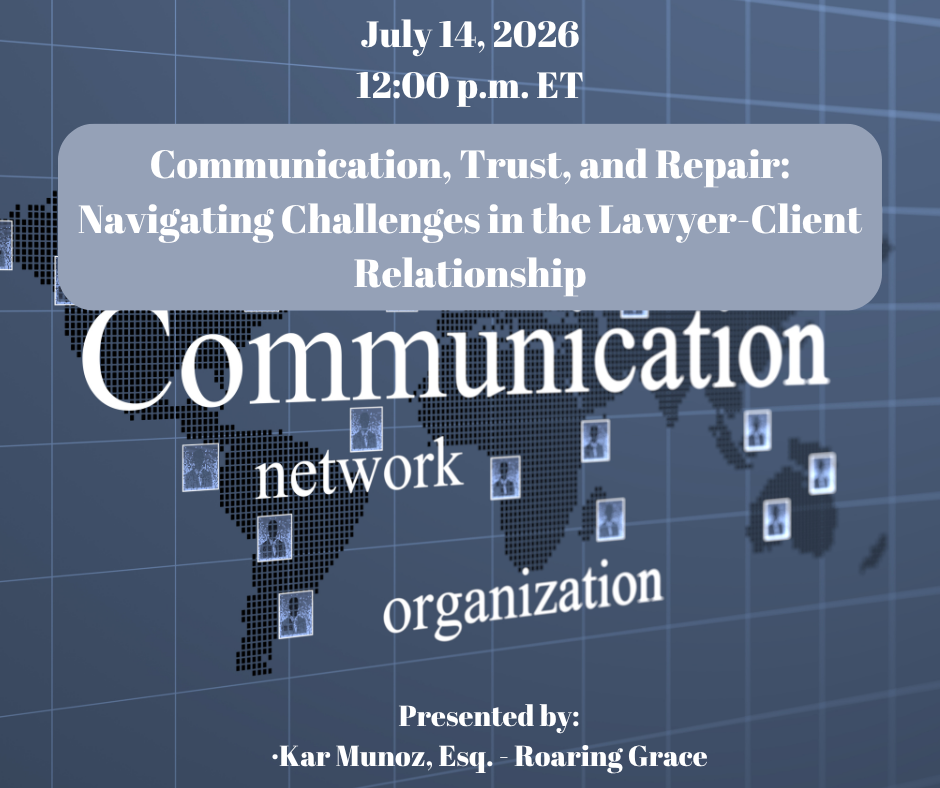
Effective representation depends on trust, communication, and responsiveness, yet these can break do...